CyberArk Identity Flows Accelerates Cybersecurity Risk Response
New Advanced Automation Capabilities and Integrations with Gurucul, Proofpoint and SentinelOne Enable Proactive Threat Protection
CyberArk (NASDAQ: CYBR), the global leader in Identity Security, today announced enhancements to its CyberArk Identity Flows orchestration solution, including new integrations with Gurucul, Proofpoint and SentinelOne. Part of the CyberArk Identity Security Platform, CyberArk Identity Flows automates risk response tasks and processes through no-code app integrations and workflows, and improves response times, efficiency and productivity.
This press release features multimedia. View the full release here: https://www.businesswire.com/news/home/20230509005209/en/
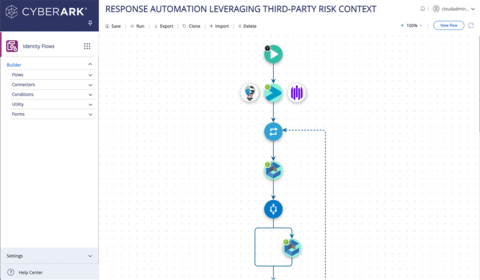
CyberArk Identity Flows increases the value of threat detection data by orchestrating rapid responses to risk. (Graphic: Business Wire)
CyberArk Identity Flows includes a user-friendly workflow builder with powerful integration and orchestration capabilities for identity-related business processes, data management and security event responses.
New features enable organizations to orchestrate complex responses to a potential threat or security event and act on the valuable data provided by threat monitoring and alerting systems. For example, when a security alert is triggered due to continued failed login attempts, users can be automatically moved into a “risky persons” group to restrict access to specific resources. This feature can also automatically notify relevant parties of the risk, create IT tickets, or take other actions based on security policies.
The new technology integrations, available on CyberArk Marketplace, expand these capabilities to work with the industry’s leading threat detection systems, including:
- Gurucul Security Analytics and Operations Platform – detects threats and provides analytics-driven risk scoring to quickly identify and prioritize new, emerging and unknown threats. CyberArk Identity Flows can gather the risk score from Gurucul and orchestrate appropriate responses and actions to reduce the manual effort associated with threat investigation and remediation while securing the associated identity(s).
- Proofpoint Targeted Attack Protection (TAP) – detects email threats and assigns a level of risk to individuals with a Very Attacked People (VAP) feature. CyberArk Identity Flows can utilize the insights provided by Proofpoint to orchestrate appropriate responses such as moving identities into different groups to change access permissions, change an authentication policy, send alerts, post notifications or create IT tickets.
- SentinelOne Singularity Platform – detects and hunts for threats across user endpoints, containers, cloud workloads and IoT devices. When risks are detected, CyberArk Identity Flows leverages that context to make decisions within workflow actions that need to take place across the identity infrastructure.
With CyberArk Identity Flows, workflows can be built in minutes through a user-friendly visual editor and thousands of pre-built connectors to more than 700 applications. CyberArk Identity Flows now also integrates with CyberArk Identity Security Intelligence, a shared service of the CyberArk Identity Security Platform that leverages user behavior analytics to detect and remediate anomalous and risky activity by employees. When high-risk behavior is detected, CyberArk Identity Flows is used to orchestrate response actions to reduce response times to attacks to minimize risk.
“Flexible automation and orchestration are critical to a proactive Identity Security program and vital to improving the security posture of our clients. That’s why we’ve been so focused on delivering new CyberArk Identity Flows innovations,” said Peretz Regev, chief product officer at CyberArk. “With these enhancements and integrations, we make it simple for organizations to use CyberArk Identity Flows to reduce IT overhead, accelerate service agility and strengthen their overall security, ultimately improving operational efficiencies.”
CyberArk Identity Flows can be purchased as a standalone solution, or as part of the CyberArk Identity Security Platform. CyberArk applies intelligent privilege controls to all identities – human and machine – with continuous threat detection and prevention across the entire identity lifecycle. With the CyberArk Identity Security Platform, organizations can enable Zero Trust and least privilege with complete visibility, enabling every identity to securely access any resource, located anywhere, from everywhere.
To learn more, please register for “Better Security with Threat Response Automation,” a webinar taking place on May 18, 2023 or visit https://www.cyberark.com/products/identity-flows/.
About CyberArk
CyberArk (NASDAQ: CYBR) is the global leader in Identity Security. Centered on privileged access management, CyberArk provides the most comprehensive security offering for any identity – human or machine – across business applications, distributed workforces, hybrid cloud workloads and throughout the DevOps lifecycle. The world’s leading organizations trust CyberArk to help secure their most critical assets. To learn more about CyberArk, visit https://www.cyberark.com, read the CyberArk blogs or follow on Twitter via @CyberArk, LinkedIn or Facebook.
Copyright © 2023 CyberArk Software. All Rights Reserved. All other brand names, product names, or trademarks belong to their respective holders.
View source version on businesswire.com: https://www.businesswire.com/news/home/20230509005209/en/
Contacts
Media Contacts:
Carissa Ryan, CyberArk
Email: press@cyberark.com
Highwire PR
Email: cyberark@highwirepr.com
Investor Relations:
Erica Smith, CyberArk
Email: ir@cyberark.com
If you believe this article contains misleading, harmful, or spam content, please let us know.
Report this articleMore News
View MoreRecent Quotes
View MoreQuotes delayed at least 20 minutes.
By accessing this page, you agree to the Privacy Policy and Terms Of Service.




