CyberArk Launches Industry’s First Identity-Centric Secure Browser
CyberArk Secure Browser Makes It Easy to Tailor Security, Privacy and Productivity Controls on Managed and Unmanaged Workforce Devices
CyberArk (NASDAQ: CYBR), the identity security company, today announced the general availability of CyberArk Secure Browser, the industry’s first identity-centric secure browser, providing enhanced security and privacy alongside a familiar, productive user experience.
This press release features multimedia. View the full release here: https://www.businesswire.com/news/home/20240327457893/en/
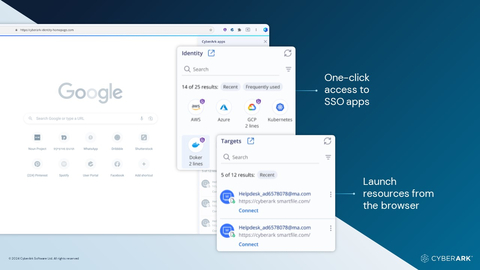
CyberArk Secure Browser provides enhanced security alongside a familiar user experience. (Graphic: Business Wire)
Backed by intelligent privilege controls and simple to deploy across devices, CyberArk Secure Browser is purpose-built for a cloud-first world, providing secure, consistent access to both on-premises resources and SaaS applications. It allows unprecedented visibility, control and governance for security teams, helping to prevent the malicious use of compromised identities, endpoints and credentials both at and beyond login. Secure Browser is a component of the CyberArk Identity Security Platform, enabling secure access for any identity — human or machine — to any resource or environment from anywhere, using any device.
“Increased usage of remote access, SaaS applications and cloud infrastructure created a security blind spot for us, prompting a rethink of our security posture and investment in tools to secure unauthorized access to critical assets via our distributed workforce,” said Chris Dove, Enterprise Architect, California Department of Finance. “Adding CyberArk Secure Browser to our existing CyberArk deployment will allow us to strictly enforce security policies without sacrificing productivity. We will be better able to safeguard our data, making sure employees can only access work systems through a secure, isolated browser that rotates passwords and keeps them from being saved – and potentially stolen.”
A March 2024 study of US office workers further highlights the browser-based cybersecurity risk exposure faced by organizations1:
- 78% use the same device to access company-confidential and sensitive information as they do for personal browsing
- 65% said that they need to violate organizational safe browsing policies to perform their role (12% “always” violated policies).
- 59% save workplace logins and passwords in the web browser used to perform their job.
Available to customers of the CyberArk Identity Security Platform, CyberArk Secure Browser safeguards the organization’s most valuable resources, enabling a secure passwordless experience, easy access to privileged information and assets and helping to prevent breaches resulting from cookie theft and session takeover attacks. Recent major security breaches and new research from CyberArk Labs demonstrates how easy it is for techniques like cookie theft to give threat actors unauthorized access to sensitive data and assets, completely bypassing authentication tools. Secure Browser can ensure that there are no cookies to steal.
CyberArk Secure Browser Addresses Key Enterprise Cybersecurity Challenges
- Secures all access – including privileged and sensitive access – from the browser
- Fully integrates with the organization’s entire Identity and Access Management and security architecture
- Provides a secure and safe way for users to access corporate resources from their own or unmanaged devices
- Separates work and personal applications and domains
- Enables easy, quick resource access for all user types, including high-risk groups
- Streamlines ability to meet regulatory and audit requirements
“The proliferation of SaaS apps, cloud-native resources and business-critical applications that are accessed from the browser introduce new and significant risks that attackers have been quick to take advantage of,” said Matt Cohen, CEO, CyberArk. “Traditional access management approaches lack the right controls at the edge to be able to see and secure the complete identity journey, end-to-end. We are excited to deliver an enhanced enterprise browser that boosts productivity and layers on additional security and privacy controls to the most frequently used application in most organizations. This is just another example of how CyberArk is extending identity security to all users no matter how they access sensitive data and assets.”
Resources
- CyberArk Labs research: Crumbled Security: Unmasking the Cookie-Stealing Malware Threat
- CyberArk Secure Browser Solution Brief: The Gateway to Securing All Identities
- Blog: Enterprise Browsers Need to Secure Identities Without Compromise
- Webinar: Mastering Browser Security for Enterprise Defense
1 Survey of 4,000 US office workers conducted by Censuswide
About CyberArk
CyberArk (NASDAQ: CYBR) is the global leader in identity security. Centered on intelligent privilege controls, CyberArk provides the most comprehensive security offering for any identity – human or machine – across business applications, distributed workforces, hybrid cloud environments and throughout the DevOps lifecycle. The world’s leading organizations trust CyberArk to help secure their most critical assets. To learn more about CyberArk, visit https://www.cyberark.com, read the CyberArk blogs or follow on LinkedIn, Twitter, Facebook or YouTube.
Copyright © 2024 CyberArk Software. All Rights Reserved. All other brand names, product names, or trademarks belong to their respective holders.
View source version on businesswire.com: https://www.businesswire.com/news/home/20240327457893/en/
Contacts
Media:
Carissa Ryan
Press@CyberArk.com
Investors:
Erica Smith
InvestorRelations@CyberArk.com
If you believe this article contains misleading, harmful, or spam content, please let us know.
Report this articleMore News
View MoreRecent Quotes
View MoreQuotes delayed at least 20 minutes.
By accessing this page, you agree to the Privacy Policy and Terms Of Service.




