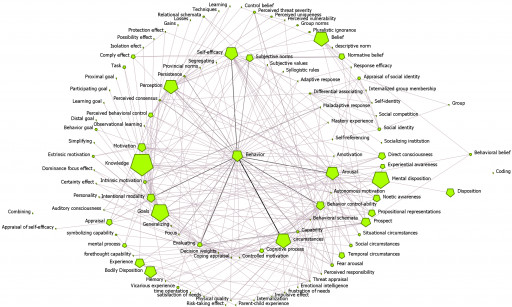
Visualization of Cybonto
A visualization of the Cybonto core ontology, reflecting the complexities of future Human Digital Twins' cognitive systems.
Tam Nguyen, CISSP and a research fellow at the University of Arizona, has published a new research paper in JMIR Publications: "Toward Human Digital Twins for Cybersecurity Simulations on the Metaverse: Ontological and Network Science Approach".
Technological revolution has familiarized the world with a new concept: the Metaverse. The Metaverse is a massive unified digital realm created from virtual and augmented reality, blockchain, social networks, cloud infrastructure, 3D networks etc. simulating the real world. With this growing digital universe, cybersecurity becomes even more important. Currently, cyber-defense strategies are still reactive and slow; while it usually takes just 15 hours for hackers to break through the defense, defenders take 200-300 days to discover a breach. In his paper, Nguyen suggests expanding the scope of Digital Twins (DTs) and Human Digital Twins (HDTs) in the Metaverse for cybersecurity defense purposes.
DTs are virtual models designed to accurately reflect physical objects like routers, servers, IoT systems. HDTs are a specialized form of DTs which can act as system users, system admins, and malicious agents. Because HDTs are completely autonomous, they can interact with other HDTs and DTs. Therefore, complex cybersecurity simulations can be played out in secured sections of the Metaverse. The key is building realistic Human Digital Twins that can think and act like real hackers/defenders.
Nguyen's recently published paper in JMIR presents a conceptual framework for running massive cybersecurity simulations on the Metaverse with HDTs. The framework relies on a novel cybersecurity behavioral ontology or 'Cybonto', which aims to enhance Human Digital Twins' cognitive systems. At the core of Cybonto, it is a collection of 108 psychology constructs and thousands of related paths based on 20 time-tested psychology theories. HDT design teams can implement Cybonto so that their HDTs can realistically mimic the thought processes and behaviors of system users, system admins, and even malicious agents. Challenging cybersecurity scenarios may then be simulated 24/7 on secured sections of the Metaverse. Simulated results may offer insights into the complex interdependent networks of systems, users, admins, and hackers. Such insights will lead to more proactive and more effective cybersecurity strategies.
Cybonto is versatile. It can be used for other purposes such as manually analyzing hackers' behaviors, and automatic analysis of behavioral-cybersecurity knowledge texts. Cybonto can also find uses beyond cybersecurity in the medical field for applied psychology training, automatic analysis of electronic health records, and virtual community psychology experiments.
Nguyen is open to further discussions at tamn@email.arizona.edu.
Press Release Service by Newswire.com
Original Source: Tam Nguyen, CISSP Announces New Research Paper: 'Toward Human Digital Twins for Cybersecurity Simulations on the Metaverse'






